Stories & Insights
Instantly Share Your Local Project: No Domain Required using Cloudflare Quick Tunnels
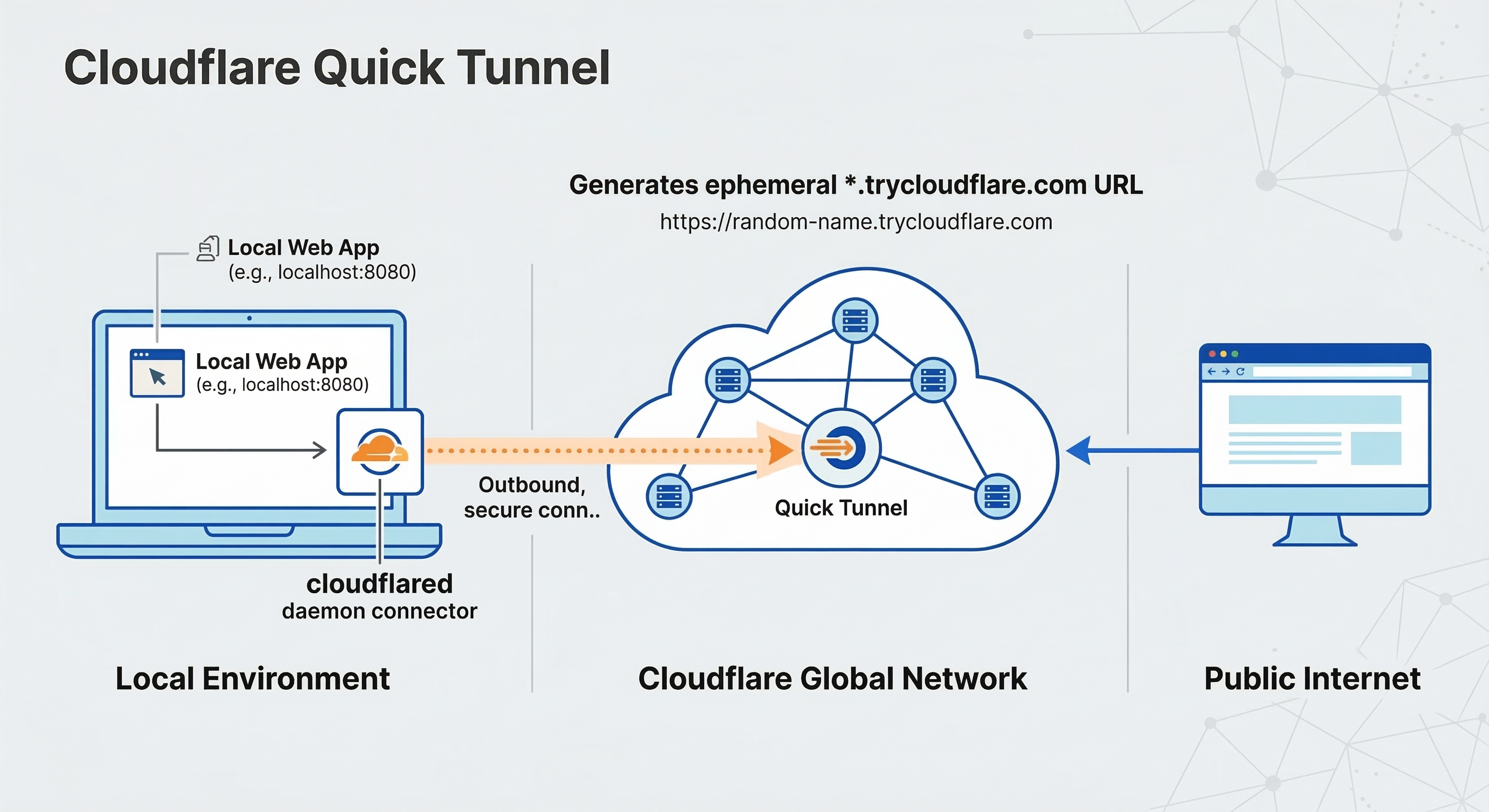
As developers, we often need to share our local work. Whether it’s showing a client a new feature, testing a webhook callback from a third-party API, or just demoing a project to a colleague, exposing localhost to the internet is a common challenge. Traditionally, this involved navigating the dark arts of router port forwarding, dealing with dynamic IPs, or paying for static IP addresses. Cloudflare Tunnel (formerly Argo Tunnel) changed this game, but often requires you to own a custom domain and configure DNS. But what if you don't have a domain yet, or just need a quick, temporary solution? Enter Cloudflare Quick Tunnels. This feature allows you to create a secure, publicly accessible URL for any local port on your machine instantly, without needing a custom domain, port forwarding, or complex configuration. You get a random, temporary trycloudflare.com subdomain that works immediately. Here is how you can spin up a public tunnel for your local machine in three simple steps. Prerequisites Before you begin, ensure you have a service running locally that you want to share (for example, a web server running on http://localhost:8080). Step 1: Install the cloudflared tool First, you need to download and install the cloudflared daemon, which acts as the bridge between your local machine and the Cloudflare network. Choose the command for your operating system: On macOS (using Homebrew): On Linux (Debian/Ubuntu): On Windows: You can download the latest .exe binary directly from the Cloudflare downloads page and add it to your system PATH. Step 2: Spin up the Tunnel Now that cloudflared is installed, you can start the tunnel with a single command. Open your terminal or command prompt and run the following, replacing 8080 with the port your local service is running on: This command tells Cloudflare: "Take the traffic destined for the URL you are about to generate and send it securely to localhost:8080 on this machine." Step 3: Access and Share your App After running the command, cloudflared will generate several lines of log output. Look closely for a section that looks like this: That’s it! Anyone in the world can now click that trycloudflare.com link and access your local application. Understanding the Architecture How does this work without touching your router settings? This diagram illustrates the flow: The cloudflared agent running on your machine establishes an outbound connection to the Cloudflare global network. When a user tries to access your temporary trycloudflare.com URL, they hit the Cloudflare edge. Cloudflare then routes that traffic through the existing secure connection directly to your local service. Because the connection is outbound from your machine, you don’t need to open any inbound ports on your router or firewall. Key Security and Usage Considerations While Quick Tunnels are incredibly convenient, it's important to understand how they differ from fully managed, named Cloudflare Tunnels: Ephemeral URLs: The trycloudflare.com URL is temporary. Every time you stop and restart the cloudflared command, you will get a completely new and random URL. This makes it perfect for quick demos, but unsuitable for production or permanent remote access. Public Access: By default, anyone who guesses or acquires your unique trycloudflare.com URL can access your local service. There is no built-in authentication for Quick Tunnels. Do not share sensitive data using this method without adding your own authentication to the local application. No Dashboard Visibility: Quick Tunnels are handled automatically. They do not appear in your Cloudflare dashboard, and you cannot apply Cloudflare Access policies or other Zero Trust features to them. Summary Cloudflare Quick Tunnels are an invaluable tool for developers needing to share local progress instantly. If you need a persistent URL, integration with the Cloudflare dashboard, or advanced Access/Security policies, you should upgrade to a Named Tunnel (which does require a custom domain on Cloudflare). But for everything else, Quick Tunnels are the fastest way to get your localhost onto the internet.
🚀 Automatically Activate Python Virtual Environments When Entering a Project Directory (Linux)
If you work on multiple Python projects, you’ve probably typed this command hundreds of times: source venv/bin/activate It’s easy to forget, and running code outside the correct environment can cause confusing bugs. In this article, you’ll learn how to automatically activate a Python virtual environment whenever you enter a specific directory—on any Linux machine or server. 🎯 Why Auto-Activate Virtual Environments? Prevents running code with the wrong dependencies Saves time and mental overhead Works seamlessly with SSH, VS Code Remote, and servers Ideal for Django, FastAPI, Flask, and data projects 🧩 How This Solution Works Bash provides a special hook called PROMPT_COMMAND that runs before each command prompt is displayed. We use this hook to: Detect your current directory Check if a virtual environment is already active Activate the environment automatically when needed 📋 Prerequisites Linux system (Ubuntu, Debian, Arch, etc.) Bash shell Python virtual environment already created Basic terminal access 🛠 Step-by-Step Setup Step 1: Open your .bashrc file nano ~/.bashrc Step 2: Add the auto-activation logic Paste the following code at the end of the file: 🔹 Replace: /full/path/to/your/project with your project directory /full/path/to/your/venv with your virtual environment path Step 3: Reload the shell configuration source ~/.bashrc ✅ What Happens Now? When you cd into your project → virtual environment activates automatically When you open a new terminal inside the project → already activated When you’re outside the project → no activation 🧪 Example Behavior 🧠 Why This Approach Is Safe ✔ No repeated activation ✔ No errors if the virtualenv is missing ✔ No performance impact ✔ Works on remote servers Multiple Projects You can duplicate the function for multiple directories or convert it into a loop. 🆚 Alternative: direnv Tools like direnv can also do this, but they require extra installation and configuration. This Bash-only approach is lightweight, portable, and dependency-free. 🧩 Supported Environments Ubuntu 20.04 / 22.04 Linux servers SSH sessions VS Code Remote SSH WSL (Linux mode) 🏁 Final Thoughts Automating virtual environment activation is a small change that dramatically improves your daily Python workflow. Once you set it up, you’ll wonder why you didn’t do it sooner.

How to Install Python 3.12 on Ubuntu 22.04

Working with ESRI Shapefiles using GDAL / OGR
This guide covers common OGR/GDAL command-line operations for working with ESRI Shapefiles and PostGIS databases, including inspection, reprojection, format conversion, querying, and database updates. Identify the Geometry Type of a Shapefile ogrinfo Bittner_BellePrairieSec8_N40_Boundary.shp This command lists layers and shows the geometry type (Polygon, Point, etc.). Get Full Details of a Shapefile (Schema + Metadata) ogrinfo -so Bittner_BellePrairieSec8_N40_Boundary.shp \ -sql "SELECT * FROM Bittner_BellePrairieSec8_N40_Boundary" -so → summary only (no feature dump) Shows fields, geometry type, and spatial reference Get Full Details of a Specific Record (by FID) ogrinfo Bittner_BellePrairieSec8_N40_Boundary.shp \ -sql "SELECT * FROM Bittner_BellePrairieSec8_N40_Boundary WHERE fid = 1" Reproject an Existing ESRI Shapefile ogr2ogr ../newShp/Bittner_BellePrairieSec8_N40_Boundary.shp \ -t_srs EPSG:4326 \ Bittner_BellePrairieSec8_N40_Boundary.shp Converts projection to WGS84 (EPSG:4326) Convert an ESRI Shapefile to GeoJSON ogr2ogr -f GeoJSON \ ../newShp/Bittner_BellePrairieSec8_N40_Boundary.json \ -t_srs EPSG:4326 \ Bittner_BellePrairieSec8_N40_Boundary.shp Select Records and Create a New Shapefile ogr2ogr ../newShp/filtered.shp \ Bittner_BellePrairieSec8_N40_Boundary.shp \ -sql "SELECT * FROM Bittner_BellePrairieSec8_N40_Boundary WHERE name = 'Apple'" Count Records in a Shapefile ogrinfo Bittner_BellePrairieSec8_N40_Boundary.shp \ -sql "SELECT COUNT(*) FROM Bittner_BellePrairieSec8_N40_Boundary" Count DISTINCT Records in a Shapefile ogrinfo Bittner_BellePrairieSec8_N40_Boundary.shp \ -sql "SELECT COUNT(DISTINCT name) FROM Bittner_BellePrairieSec8_N40_Boundary" Clip Spatial Data (Points within Polygon) ogr2ogr ../newShp/clipped.shp \ ../esridata/points.shp \ -clipsrc Bittner_BellePrairieSec8_N40_Boundary.shp Note: Input geometry must be POINT Clip geometry must be POLYGON OGR & PostGIS Queries Connect to PostGIS and List Tables ogrinfo PG:"host=localhost port=5432 user=postgres password=postgres dbname=landgate_local_db1" Extract Data from PostGIS to GeoJSON ogr2ogr -f GeoJSON \ ../newShp/trees.geojson \ PG:"host=localhost port=5432 user=postgres password=postgres dbname=landgate_local_db1" \ -sql "SELECT * FROM bittner_belleprairiesec8_n40_boundary" Extract Data from PostGIS to an ESRI Shapefile ogr2ogr -f "ESRI Shapefile" \ ../newShp/trees.shp \ PG:"host=localhost port=5432 user=postgres password=postgres dbname=landgate_local_db1" \ -sql "SELECT * FROM bittner_belleprairiesec8_n40_boundary" Extract & Reproject PostGIS Data to EPSG:32643 ogr2ogr -f "ESRI Shapefile" \ ../newShp/trees.shp \ -t_srs EPSG:32643 \ PG:"host=localhost port=5432 user=postgres password=postgres dbname=landgate_local_db1" \ -sql "SELECT * FROM bittner_belleprairiesec8_n40_boundary" Extract Specific Fields & Records from PostGIS ogr2ogr -f "ESRI Shapefile" \ ../newShp/trees.shp \ -select name \ PG:"host=localhost port=5432 user=postgres password=postgres dbname=landgate_local_db1" \ -sql "SELECT * FROM bittner_belleprairiesec8_n40_boundary WHERE name = 'mango'" Insert Shapefile Records into PostGIS ogr2ogr -f PostgreSQL \ PG:"host=localhost port=5432 user=postgres password=postgres dbname=landgate_local_db1" \ Bittner_BellePrairieSec8_N40_Boundary.shp Add a New Column to a PostGIS Table ogrinfo PG:"host=localhost port=5432 user=postgres password=postgres dbname=landgate_local_db1" \ -sql "ALTER TABLE bittner_belleprairiesec8_n40_boundary ADD COLUMN surveyor TEXT" Update PostGIS Table Records Using WHERE Clause ogrinfo PG:"host=localhost port=5432 user=postgres password=postgres dbname=landgate_local_db1" \ -dialect SQLite \ -sql "UPDATE bittner_belleprairiesec8_n40_boundary SET surveyor = 'Akash' WHERE gid = 1" Conclusion OGR/GDAL provides a powerful CLI for: Inspecting spatial data Reprojecting layers Converting formats Querying spatial datasets Integrating Shapefiles with PostGIS These commands are essential for GIS developers, data engineers, and backend developers working with spatial data.

Step-by-Step Guide to Reset PostgreSQL User Password for Specific Version
To reset the password for a PostgreSQL user for a specific version of PostgreSQL on your Ubuntu system, you'll need to follow these steps. The process involves connecting to the correct instance of PostgreSQL and utilizing the psql command-line interface. 1) Identify the Correct PostgreSQL Version and Port: $ pg_lsclusters 2) Connect to the Correct Version: $ sudo -u postgres psql -p PORT 3) Change the User Password: Once connected to the PostgreSQL prompt, you can reset the password of a specific PostgreSQL user by executing the following SQL command: $ ALTER USER your_username WITH PASSWORD 'new_password'; 4) Exit the PostgreSQL Shell: After you successfully change the password, you can exit the psql prompt by typing: $ \q Notes: Make sure that the user you are trying to modify exists in that specific PostgreSQL instance. You can check existing users by running\duin the PostgreSQL prompt. If you encounter permission issues while connecting, ensure that you’re using the correct PostgreSQL superuser (usually postgres) to execute the ALTER USERcommand. If PostgreSQL is configured to use the peer authentication method, you may have to change the authentication method in the pg_hba.conf file for the postgres user to md5in order to use password authentication. Summary By connecting to the specific PostgreSQL version and using the appropriate SQL command, you can easily reset any user's password on your Ubuntu system. Always make sure to use a secure password, especially in production environments.
